Multi-Factor Authentication (MFA)
MFA protects your account by requiring a second factor of authentication, reducing the risk of phishing or leaked passwords.
Atlar supports hardware security keys (such as YubiKey or Google Titan), your device's built-in passkey authenticator (such as Face ID or Windows Hello), or a passkey-compatible password manager (such as Apple Passwords or Google Password Manager). These methods add a strong extra layer of security beyond a password.
Add Multi-Factor Authenticators
- Go to My Account by clicking your name in the bottom-left corner of the dashboard.
- Under Multi-Factor Authentication, add a new authenticator such as a hardware key or passkey.
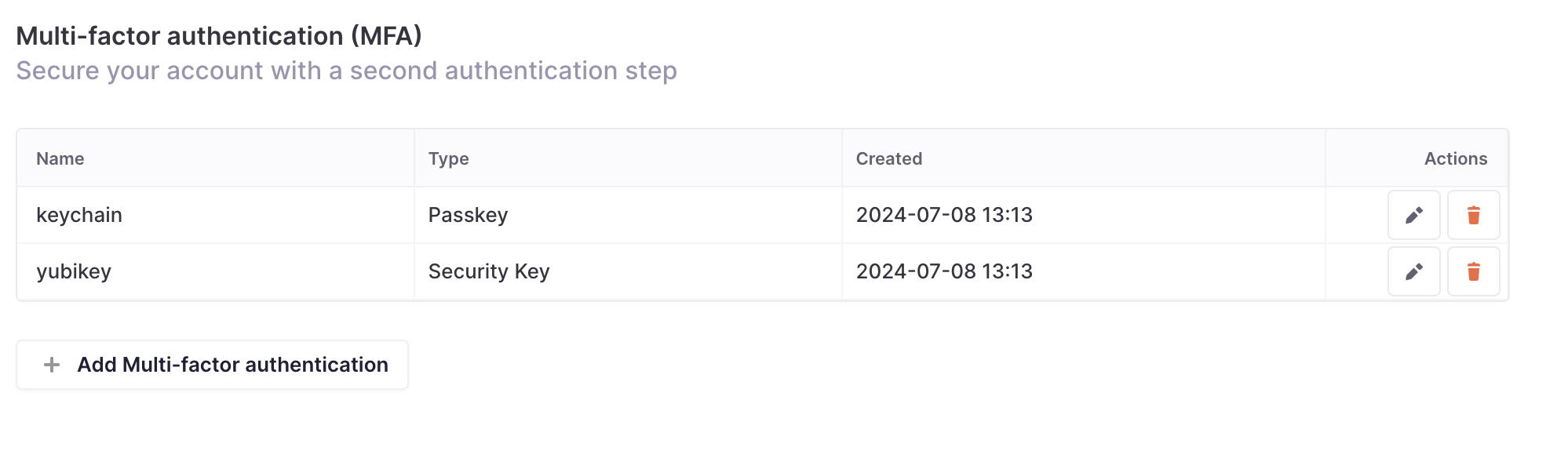
The MFA settings available under My Account page.
Supported Authenticators
Any authenticator that supports WebAuthn can be used. Some popular options are listed below.
Hardware security key
Passkey
- 1Password
- Apple passwords
- Bitwarden
- Chrome on Mac
- Chromium browser
- Dashlane
- Google Password Manager
- KeePassXC
- Keeper
- LastPass
- NordPass
- Proton Pass
- Samsung Pass
- Windows Hello
Best practices
- Configure more than one MFA option as a backup in case one is lost or destroyed.
- Use a hardware security key for added portability and convenience.
- Regularly review and update your MFA options.
- Keep security keys personal, just like passwords—never share them.
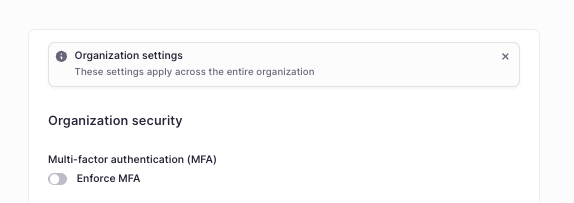
Require MFA for your organization
To require MFA for your organization you can enforce it by navigating to Settings > Organization. Under the Multi-factor authentication (MFA) section you can select Enforce MFA.
Recover from a lost MFA device
To avoid lockouts:
- Add multiple MFA options so you can log in using an alternative method.
- Remove any lost MFA option immediately to protect your account.
If all MFA devices are lost and you are locked out, contact Atlar support to manually disable MFA. This process includes a verification step to ensure only authorized users regain access to the Atlar web app.
Troubleshooting
- For security reasons, Time-based One-Time Password (TOTP) authenticators (such as Authy and Google Authenticator) are not supported. Unlike hardware security keys and passkeys, TOTP codes can be stolen through phishing and used by an attacker to gain access to your account.
- Microsoft Authenticator and Okta Verify are not supported for passkeys. These apps only store passkeys for use with their own platforms — they cannot be used as a passkey provider for other sites or applications.
Updated 2 months ago
